LAST UPDATE — 09-25-2025
In the contemporary digital world, data is the most important asset for both individuals and organizations. Therefore, implementing a strong data protection plan is a critical business necessity. These data protection plans must follow a multi-layered approach by including the security models. The security models act as guidance to maintain the confidentiality, integrity and availability (CIA triad) within the systems. When it comes to cybersecurity compliance, knowing the right cyber security model can make all the difference. These information security models help protect sensitive data, support secure systems, and ensure compliance with rules and standards. But not all models work the same.
That’s why a strong security model comparison for enterprise environments is essential. You need to pick the one that fits your needs and keeps your data safe. For example, many experts look at Bell-LaPadula vs Clark-Wilson to understand how access and control work in different settings. These two classic models serve very different goals. And today, with cloud services on the rise, businesses also need to explore modern security models for cloud compliance. Each model comes with its strengths, limits, and use cases. In addition, the rise of Zero Trust frameworks, attribute-based access control (ABAC), and continuous threat exposure management have made security models more dynamic and adaptive. Organizations are now blending traditional and modern approaches to safeguard against insider threats, AI-driven attacks, and regulatory non-compliance.
This blog provides you with a thorough understanding of different security models in cyber security. Furthermore, it discusses their practical applications and associated benefits in protecting the digital infrastructures against potential threats. Moreover, it provides you with detailed knowledge regarding the complex technicalities of security models.
Tl; DR:
Concern: Organizations face increasing cyber threats, regulatory pressure, and complex IT environments. Choosing the wrong security model or failing to implement it correctly can expose sensitive data, weaken defenses, and lead to compliance violations.
Overview: Security models like Bell-LaPadula, Biba, Clark-Wilson, HRU, and Chinese Wall provide structured frameworks to enforce confidentiality, integrity, and availability. They guide access controls, data protection, and compliance with global standards. However, each model has specific strengths and limitations depending on business needs.
Solution: By evaluating risks, understanding each model, and aligning with frameworks like NIST or ISO 27001, organizations can adopt the right security model. Expert guidance ensures proper implementation, enabling proactive risk management, regulatory compliance, and robust data protection for evolving digital ecosystems.
WHAT IS SECURITY MODELS?
Information security models are organized frameworks that specify how different security measures should be included in a company’s system to guard against unwanted access and alteration. To clarify, it offers detailed guidance for developing, implementing into practice, and managing internal controls on access, including intrusion detection systems, firewalls, and encryption. Therefore, a security model helps prevent data breaches and safeguard critical information from potential threats.
Here’s an overview of the components within these IT security models:
- Subjects: Subjects are the active objects that exist within the system and interact with data. For example, subjects include users, processes, and applications. Additionally, they access, change, and control information within the system.
- Objects: Objects are the static and protected information present within the system. These are the important elements that must be safeguarded against unauthorized access or changes. If not, it will lead to security risks and data breaches. For example, objects are data, files and sensitive information stored in the system.
- Operations: Operations are the different processes performed on objects. These include reading, writing, or executing functions. To ensure that only authorized subjects can perform these operations, we carefully monitor each operation. Thereby, ensuring integrity and confidentiality.
- Access Control Mechanisms: Access control mechanisms outline standard guidelines for operations between subjects and objects. In particular, these mechanisms make sure that only authorized subjects are provided access to sensitive information, leading to a secured environment.
- Security Policies: Security policies are solid guidelines that outline acceptable security practices within the system. These policies define the boundaries for secure behavior, reducing risks by confirming that security measures are consistently applied and aligned with business objectives.
Today, modern security models also integrate identity management, behavioral analytics, and adaptive authentication. This ensures that access decisions are not static but instead influenced by contextual factors such as device health, user location, and risk level.
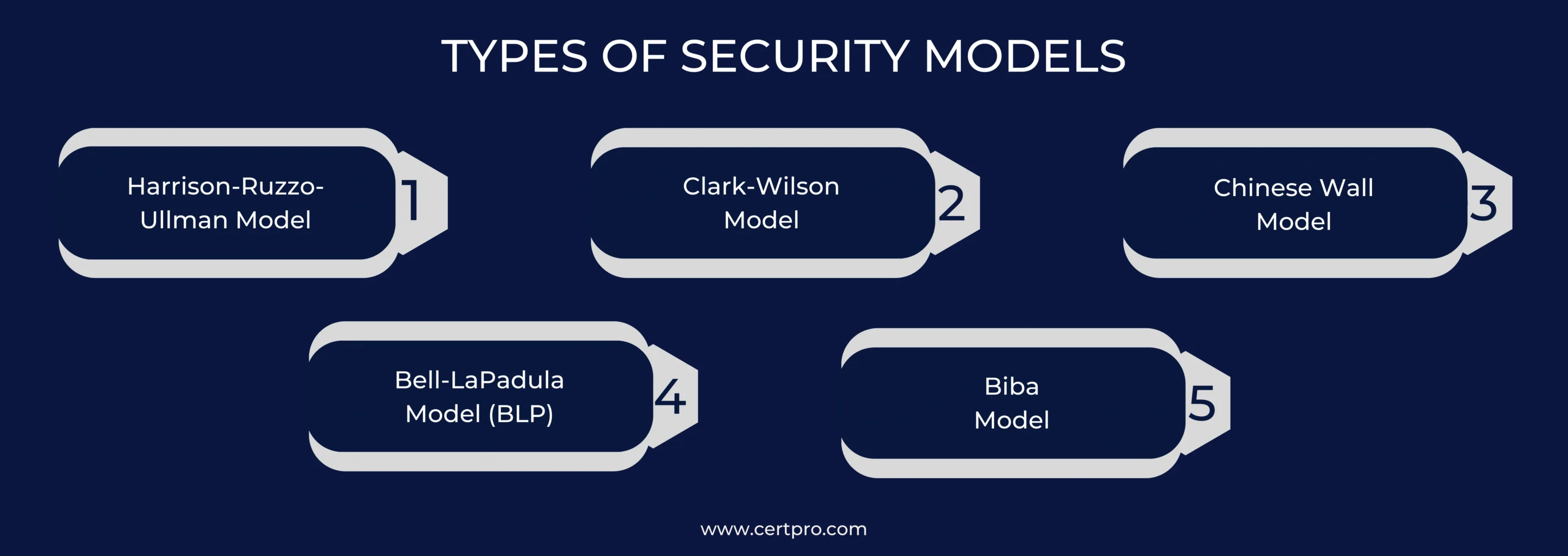
TYPES OF INFORMATION SECURITY MODELS
The field of security is vast and requires different types of security models to address various needs. Here are some important IT models that help organizations keep their information safe:
- Harrison-Ruzzo-Ullman Model (HRU): The HRU Model is an extension of the Bell-LaPadula (BLP) Model. It adds a system that allows changes to access rights, which the BLP model doesn’t do. It uses an access matrix, where users (called subjects) can do certain actions on objects (like files or data). This data security model helps businesses manage access rights more flexibly while keeping information secure.
- Clark-Wilson Model: The Clark-Wilson Model focuses on keeping data accurate and unaltered. It separates data into two categories: safe data (constrained data items) and unsafe data (unconstrained data items). It only allows trusted actions to change the safe data, making sure no one can tamper with important information.
- Chinese Wall Model: The Chinese Wall Model helps avoid conflicts of interest. It stops users from accessing data that could cause a conflict, like confidential information from two competing companies. It is also called the Brewer and Nash model.
- Bell-LaPadula Model (BLP): The Bell-LaPadula Model focuses on protecting sensitive information and ensuring confidentiality. It has established three key access rules and security levels known as top secret, secret, and confidential. This model helps control how information is handled at different security levels and ensures that sensitive data is kept secure.
- Biba Model: The Biba Model focuses on making sure data stays accurate and unaltered. It works in the opposite way to the Bell-LaPadula Model, stopping changes to data instead of restricting access. Further, this model focuses more on data integrity, which is not covered by the Bell-LaPadula model.
- Zero Trust Model: Zero Trust works on the principle of “never trust, always verify.” It requires continuous authentication, least-privilege access, and microsegmentation of networks. Unlike traditional models, it assumes no implicit trust within the system and is widely adopted in cloud and hybrid environments.
- Attribute-Based Access Control (ABAC): ABAC extends role-based models by considering attributes like user role, time, device, and location before granting access. It is highly flexible and suitable for dynamic, large-scale systems.
By understanding these models, businesses can pick the best one to suit their needs and protect their information.
BENEFITS OF USING SECURITY MODELS
Using different security models can be a great way to protect your organization from cyber threats. Let’s break down the key benefits:
- Better Protection By using multiple security models, an organization creates layers of protection. Think of it like building a fence with multiple gates—each one adds an extra line of defense. This helps lower the chances of hackers getting in or unauthorized access happening.
- Regulatory Compliance: Many security models are designed to help businesses meet laws and industry rules. By using these models, companies can show they’re serious about protecting sensitive data and meeting all the legal requirements. This guarantees that they are adhering to all regulatory requirements.
- Proactive Risk Management: Security models also help organizations spot problems before they become major threats. By using well-established models, businesses can quickly identify potential risks and take action to prevent them. This risk management approach helps avoid human errors and insider threats down the line.
- Operational Efficiency: When companies follow security models, it streamlines how they handle security. These models give businesses a clear set of guidelines, which saves time and effort in protecting their systems. As a result, organizations can work more efficiently, with fewer mistakes or delays. It can also help firms simplify the onboarding and offboarding of users.
- Informed Decision-Making: When an organization understands different security models, it can make better decisions about how to protect its systems. Knowing the strengths and weaknesses of each model allows companies to choose the one that fits their needs best—helping them build a stronger, more tailored defense.
Additionally, modern models such as Zero Trust and ABAC support continuous monitoring and automation, which help organizations respond faster to evolving threats and maintain long-term resilience.
WHY DO YOU NEED THE RIGHT SECURITY MODEL FOR COMPLIANCE?
Security models are really useful, but picking the right one is key for them to work well. Let’s break down the steps you need to take to choose the best security model for your needs:
- Evaluate the Requirements: The first step is to fully understand your organization’s security requirements. This means to consider factors like the laws and regulations you must follow, how sensitive your data is, and how much risk your organization can handle.
- Conduct Threat Analysis: It’s important to identify the potential threats in your organization. Evaluate past attacks and current trends in cybersecurity. This step helps you understand whether you are dealing with new threats or vulnerabilities present in your current system.
- Recognize Each Security Model: There are different security models, and each has its own strengths. For example, models like Bell-LaPadula, Biba, Clark-Wilson, and Role-Based Access Control (RBAC) all focus on protecting different parts of your system.
- Determine Requirements with Models: Once you understand the information security models, compare them to your needs. Analyze whether it is simple to implement and suitable for your business and data security requirements.
- Examine Industry Standards: Research guidelines like the NIST Cybersecurity Framework, ISO/IEC 27001, or PCI DSS to understand what they recommend. Moreover, these frameworks provide trusted advice on building strong security systems.
- Seek Professional Guidance: Don’t hesitate to speak with experts who have experience with every security model. In particular, it helps you avoid common mistakes and make better choices.
- Availability of Resources: When choosing a security model, it’s important to consider your budget and resources. Furthermore, make sure the model fits within your financial and staffing limitations.
- Pilot Experiments: Before fully implementing your security model, it’s better to run a small pilot program. Consequently, it lets you see how the model works in real time.
Compliance bodies now emphasize traceability and accountability, so organizations must ensure that chosen security models provide audit logs, access records, and documented enforcement of policies to demonstrate adherence during assessments.
APPLICATIONS OF SECURITY MODELS
A security model has wide-ranging applications across different domains, serving critical functions such as
Network Security: Consider network security as constructing a strong barrier around your network. Plus, implementing firewalls helps control the entry and exit points of the network. The security models in cyber security outlines the rules for this procedure. Similarly, systems that detect intrusions use these cyber security models to mitigate threats before their escalation. Furthermore, with Access Control Lists (ACLs), we can ensure the safety of the crucial network resources.
Operating Systems: Operating systems also rely on security frameworks to protect your information. Also, these frameworks use models to decide who can access system resources, like files or settings. Additionally, it helps keep personal data secure and prevents unauthorized users from accessing your system.
Cloud Computing: Security is also crucial for data stored in your cloud. Cloud data providers use a data security model to protect your data, ensuring its safety and security. Moreover, these cyber security models set up strong rules for privacy and data protection, so you can trust that your information is safe and only accessible by you and people authorized by you.
Application Security: Every time you use an app, it must be secure. Accordingly, developers use a kind of security model to build strong defenses into their applications, protecting them from hackers and potential threats. To clarify, companies use these information security models during the app-building process. Thereby ensuring that their apps are safe and won’t put your personal information at risk.
Data Security: Data security is all about keeping sensitive information safe from unauthorized access. In this context, security models provide a roadmap for how to protect this data. Accordingly, they implement safety measures like data encryption and access controls.
Identity and Access Management (IAM): Modern IAM systems are built on security models such as RBAC, ABAC, and Zero Trust to ensure continuous authentication, just-in-time access, and least privilege enforcement.
Supply Chain Security: Security models are increasingly applied to vendor management and software supply chains, where trust boundaries are critical for avoiding third-party risks.
CHOOSE YOUR RIGHT SECURITY MODEL UNDER CERTPRO’S PROFESSIONAL GUIDANCE
So, we can say that selecting the appropriate cyber security models may help companies improve their defenses, safeguard their information, and build lasting credibility. As technology evolves, staying current with the latest information security models becomes more important than ever. However, picking the right strategies can be challenging. Many organizations, especially startups, feel overwhelmed by the different types of security models and the technical decisions involved. The growing list of IT security models often adds to this confusion, making it hard to decide what fits best.
This highlights the clear need for expert guidance and practical support. A reliable audit partner with deep industry knowledge can help cut through the noise and provide clarity. That’s where CertPro steps in. We are a global auditing firm with over ten years of experience in compliance and cybersecurity. Our experts carefully assess your data practices and guide you in choosing the most effective security model. Let’s secure your systems together.
FAQ
What are the four main types of security in cybersecurity?
The four main types of security are network security, information security, application security, and operational security. Together, they protect data, systems, and infrastructure from unauthorized access, cyberattacks, and insider threats across different environments.
What is the CIA triad in information security?
The CIA triad stands for confidentiality, integrity, and availability. It forms the foundation of information security, ensuring sensitive data is protected, remains accurate, and is accessible only to authorized users when needed.
What are the seven layers of cybersecurity?
The seven layers of cybersecurity include physical security, network security, endpoint security, application security, data security, user education, and operational security. Together, they create a layered defense strategy against evolving cyber threats.
What is AI cybersecurity and why is it important?
AI cybersecurity uses artificial intelligence to detect threats, automate defense, and predict attacks. It enhances traditional security by identifying patterns, anomalies, and vulnerabilities faster than humans, making it critical in today’s evolving cyber landscape.
What is cloud security in cybersecurity?
Cloud security is the practice of protecting data, applications, and systems hosted on cloud platforms. It uses encryption, access control, and compliance measures to secure workloads, ensuring data privacy and resilience against breaches.

About the Author
NICOLENE KRUGER
Nicolene Kruger, Regional Manager in South Africa, is an experienced Legal Counsel with expertise in compliance and auditing. Her strategic, solution-driven approach aligns legal standards with business objectives, ensuring seamless adherence to regulations.
GRC IN CYBERSECURITY: WHAT IT MEANS AND WHY IT MATTERS IN 2026
In 2026, the pressure on companies to manage cyber risk responsibly has never been greater. Regulators demand structured controls, boards want clear risk reporting, and threat actors are becoming more sophisticated. Against this backdrop, GRC in cybersecurity has...
HOW COMPLIANCE AUDIT SOFTWARE IMPROVES AUDIT READINESS
Today, most companies deal with a growing number of compliance regulations. From data privacy standards to security frameworks like SOC 2 and ISO 27001, the list of compliance obligations keeps expanding. At the same time, regulators and external auditors now expect...
Compliance Best Practices in 2026: How to stay ahead of regulatory changes
Why is the implementation of compliance best practices critical for 2026? Compliance in 2026 demands operational proof, not the documentation intent. Regulations change faster, audit scrutiny is higher, and reporting timelines are tighter across privacy,...